Phishing - Don't Take The Bait
What is Phishing?
Typically, a fraudulent email message appearing to come from legitimate enterprises (e.g., an accredited university, an internet service provider, banks, etc). These messages usually direct a user to a spoofed website or otherwise get a user to divulge private information such as, account updates, passphrases, or credit card information.
Phishing emails are one of the most common cybersecurity threats. With about 319 billion emails sent and received each day, users need to be on high alert for phishing attacks.
According to Proofpoint’s 2021 State of the Phish report, 75% of organizations around the world experienced a phishing attack in 2020. 74% of attacks targeting US businesses succeeded.
But knowing that phishing emails are out there and dangerous is not enough. It’s important to be able to recognize one. Here are some tips from the University of Cincinnati's Office of Information Security.
Spear Phishing
UC faculty, staff, and students receive multiple spear phishing attempts each week. Spear phishing targets a particular group (e.g., members of the UC community) in order to trick recipients into providing personal information or clicking on attachments, or links in the email in order to gain access to a system or data.
Spoofing
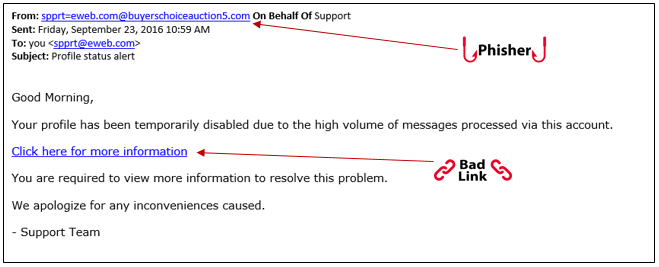
Email spoofing is the forgery of an email so that messages appear to have originated from someone or somewhere other than the actual source. Email spoofing is a tactic used in phishing attempts because users are more likely to open an email when they think it has been sent by a legitimate source. The goal of email spoofing is to get users to open, and possibly even respond to a solicitation.
How to identify a phishing attempt
Users can identify a phishing attempt by looking for email messages that create a sense of urgency, request sensitive data, or contain links that do not appear to match legitimate resources for the organization that is contacting the user.
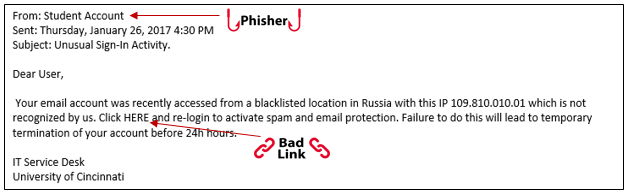
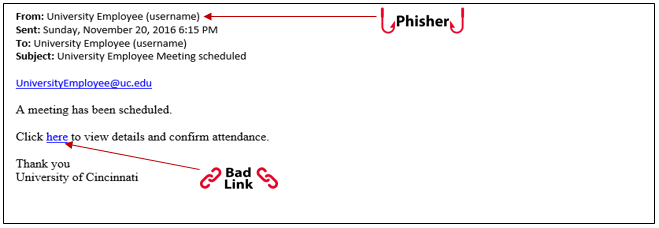
An urgent phishing email is designed to get you to act fast. It might tell you that your account was hacked or is going to be deactivated. Unfortunately, urgent phishing messages are common. Attempts that invoke strong emotion have a high success rate of luring unknowing users in.
Phishing emails can also ask you to verify your account by logging into a (fake) webpage or clicking a button to update your credentials. These types of emails can collect your username and password, allowing a hacker to gain instant access to your account information.
-Examples below:
Help! I might be getting phished. What should I do?
If you think you have received a phishing email, it’s important to slow down and examine it carefully. Remember, phishing emails deliver file attachments that can infect your computer with harmful software, or have you unknowingly share username and password information.
- First, look at the sender and domain of the email address.
- Hover over any links and see where they might direct you to.
- Other phishy identifiers might be misspelled words, incorrect dates or odd requests.
If you receive an email that appears suspicious or unusual in any way, we recommended you report it to infosec@ucmail.uc.edu, the UC Office of Information Security. From there, OIS will examine the email and advise you to take further steps if necessary.
Need IT Help?
- Get how-to instructions in the IT@UC Knowledge Base.
- Submit a ticket.
- Or, call the IT@UC Service Desk.
- From a personal phone, dial 513-556-HELP (4357) or 866-397-3382; select option 2.
- From a university phone on campus, dial 6-HELP (4357); select option 2.
- From a personal phone, dial 513-556-HELP (4357) or 866-397-3382; select option 2.